How to check md5 hash through Total Commander + MD5 Instruction File Checker

MD5 Message Digest 5 is a 128-bit hash algorithm developed by Professor Ronald L. Rivest of the Massachusetts Institute of Technology (MIT) in 1991. It is intended for creation of "prints" or digests of the message of any length and the subsequent check of their authenticity.
The MD5 algorithm is vulnerable to some attacks, for example, it is possible to create two messages with the same hash sum, so its use is not recommended. Alternatives are the algorithms of the SHA-2 family.
The scheme of work of algorithm MD5
The input of the algorithm receives an input data stream, the hash of which must be found. The length of the message can be any (including zero). We write down the length of the message in L. This number is an integer and non-negative. The multiplicity of any number is optional. After the data is received, the process of preparing the flow for calculations is in progress.
Comparison of MD5 and MD4
The MD5 algorithm is derived from MD4. Another round was added to the new algorithm, now there are 4 instead of 3 in MD4. A new constant was added in order to minimize the effect of the input message, in each round at each step and each time the constant is different, it is summed with the result of F and the data block. The function G = XZ v (Y not (Z)) has been changed instead of (XY v XZ v YZ). The result of each step is added to the result of the previous step, because of this, a faster change in the result occurs. The order of work with input words in rounds 2 and 3 has changed.
MD5 hashes
The hash contains 128 bits (16 bytes) and is usually represented as a sequence of 32 hexadecimal digits.
A few examples of the hash: MD5("md5") = 1bc29b36f623ba82aaf6724fd3b16718
Even a small change in the input message (in our case, one bit: ASCII character "5" with code 0x35 16 = 00011010 1 2 is replaced by the symbol "4" with code 0x34 16 = 00011010 0 2 ) results in a complete hash change. This property of the algorithm is called the avalanche effect.
MD5("md4") = c93d3bf7a7c4afe94b64e30c2ce39f4f Example MD5 hash for a "null" string:
MD5("") = d41d8cd98f00b204e9800998ecf8427e How to check md5 Total Commander
We often download various programs on the network, iso disk images, etc. And when we have already downloaded everything, unpacked it and installed it, we notice that something is not working right. And the matter was that during downloading some file lost one byte or more. But the program will no longer work correctly. And to avoid this, immediately after uploading we check the checksum (usually it is shown by those who upload the file to the network). If it differs, then the archive downloaded downloaded.
I've dealt with hash applications md5 quite a lot, and here we will not breed blah blah on this topic, because we just want to know How to check md5 - checksum and compare it.
If there is no possibility to use the utility, I think the total commander is for everyone.
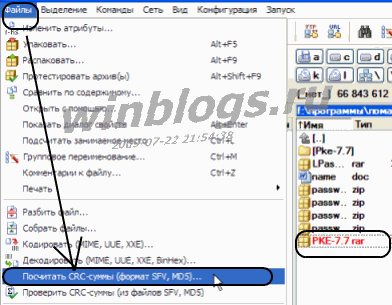
Select the file you need to check, then go File -> Calculate CRC-sums (SFV, MD5 format) ...
A window like this will pop up, tick MD5, ok
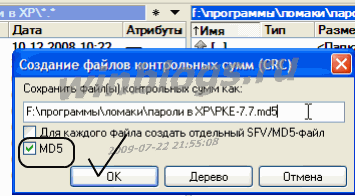
Next to the fashim file, one more will be created, with the same name and extension md5.
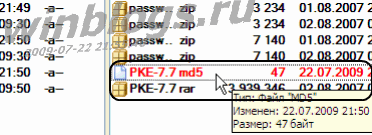
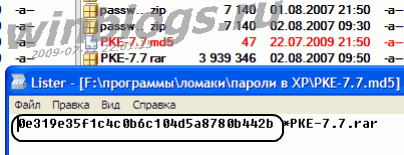
Select it and open it with the F3 key, see the checksum. That's how you can check md5 with Total Commander.
A quick guide to working with MD5 File Checker
To make sure that the downloaded file is identical to the file on the server, you need to compare their checksums. For this purpose, you can use the algorithm for calculating checksums md5.
When you add a cartoon to the server, it calculates this same checksum, you can see it on the information page about the cartoon.
To calculate this checksum already for the downloaded file on your computer, use the special program MD5 File Checker .
The program does not require installation. For users of Linux, Unix, MacOS and other operating systems, you can see similar programs directly in your OS.
Run the program. On the page with any cartoon in the block of information about the cartoon, we find the field with the checksum md5 and copy it to the clipboard.
- We paste it into the field for check # 2.
- Choose the file you want to check in the field number 1.
- We press the button "Check".
- As a result, we receive a message with the result of the program.
For example, "MD5 sum of the file coincides with the checksum - everything is OK.
The file is not corrupt "or" MD5 file sum does not match the checksum. The file may be corrupt. "Draw conclusions.
The additional possibility of the program is the calculation of the checksum md5 for an arbitrary file and its output to the user.

 Download MD5 File Checker [Md5: ac2038ecf3cb2a6e0d7fc3c7dbf5b9f7]
Download MD5 File Checker [Md5: ac2038ecf3cb2a6e0d7fc3c7dbf5b9f7] 


Comments
Commenting on, remember that the content and tone of your message can hurt the feelings of real people, show respect and tolerance to your interlocutors even if you do not share their opinion, your behavior in the conditions of freedom of expression and anonymity provided by the Internet, changes Not only virtual, but also the real world. All comments are hidden from the index, spam is controlled.