Sniffers
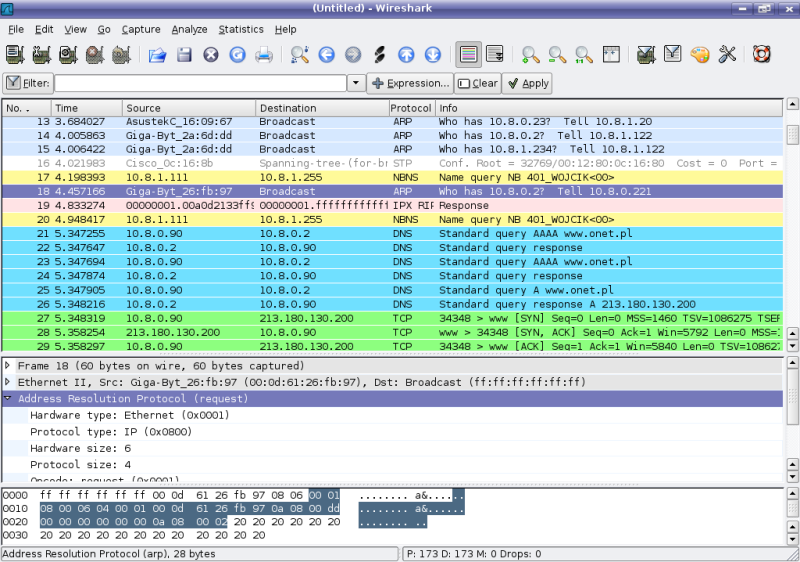
Sniffer Wireshark (formerly Ethereal)
Traffic analyzer, or sniff (from sniff to sniff) - a program or device for intercepting and analyzing network traffic (its and / or someone else's).
Sniffer can only analyze what passes through his network card. Within one segment of an Ethernet network, all packets are sent to all machines, because of this, it is possible to intercept other people's information. The use of switches (switch, switch-hub) and their competent configuration is already a protection against listening. Between segments, information is transferred through switches. Packet switching is a form of transmission in which data broken into individual packets can be forwarded from the source point to the destination by different routes. So if someone in another segment sends any packets inside it, then the switch will not send this data to your segment.
Interception of traffic can be carried out:
- The usual "listening" of the network interface (the method is effective when used in the segment of hubs instead of switches (switches), otherwise the method is ineffective, since only certain frames fall on the sniffer);
- Connecting the sniffer to the channel rupture;
- Branch (software or hardware) traffic and sending its copy to the sniffer (Network tap);
- Through the analysis of spurious electromagnetic emissions and thus the restoration of the monitored traffic;
- Through an attack on the channel (2) (MAC-spoofing) or network (3) level (IP-spoofing), which leads to redirecting the victim's traffic or all segment traffic to the sniffer and then returning traffic to the proper address.
The content of the article
Sniffers are progs that intercept all network traffic. Sniffers are useful for diagnosing the network (for admins) and for intercepting passwords (understandably for whom  ). For example, if you got access to one network machine and installed a sniffer there, then soon all the passwords from their subnet will be yours. Sniffers put the network card in the listening mode (PROMISC). That is, they receive all the packets. In the locale you can intercept all sent packets from all machines (if you are not separated by any hubs), since there is a practice of broadcasting. Sniffers can intercept all packets (which is very inconvenient, the log file is overwhelmed quickly, but for more detailed analysis of the network itself) or only the first bytes from any ftp, telnet, pop3, etc. (This is the most fun, usually in the first 100 bytes there is a name and password
). For example, if you got access to one network machine and installed a sniffer there, then soon all the passwords from their subnet will be yours. Sniffers put the network card in the listening mode (PROMISC). That is, they receive all the packets. In the locale you can intercept all sent packets from all machines (if you are not separated by any hubs), since there is a practice of broadcasting. Sniffers can intercept all packets (which is very inconvenient, the log file is overwhelmed quickly, but for more detailed analysis of the network itself) or only the first bytes from any ftp, telnet, pop3, etc. (This is the most fun, usually in the first 100 bytes there is a name and password  ). Sniffers are now divorced ... Many sniffers are both under Unix, and under Windows (even under DOS is
). Sniffers are now divorced ... Many sniffers are both under Unix, and under Windows (even under DOS is  ). Sniffers can only support a specific axis (for example linux_sniffer.c, which supports Linux
). Sniffers can only support a specific axis (for example linux_sniffer.c, which supports Linux  ), Or several (for example, Sniffit, works with BSD, Linux, Solaris). Sniffers are so relieved that passwords are transmitted over the network in clear text. There are a lot of such services. This is telnet, ftp, pop3, www, etc. These services are used by a lot of people
), Or several (for example, Sniffit, works with BSD, Linux, Solaris). Sniffers are so relieved that passwords are transmitted over the network in clear text. There are a lot of such services. This is telnet, ftp, pop3, www, etc. These services are used by a lot of people  . After the sniffers boom, various encryption algorithms for these protocols began to appear. SSH appeared (an alternative to telnet, which supports encryption), SSL (Secure Socket Layer - a development of Netscape, capable of encrypting a www session). There were all kinds of Kerberous, VPN (Virtual Private Network). Some AntiSniffs were involved, ifstatus, etc. But this did not radically change the situation. Services that use plain text password transfer are used throughout
. After the sniffers boom, various encryption algorithms for these protocols began to appear. SSH appeared (an alternative to telnet, which supports encryption), SSL (Secure Socket Layer - a development of Netscape, capable of encrypting a www session). There were all kinds of Kerberous, VPN (Virtual Private Network). Some AntiSniffs were involved, ifstatus, etc. But this did not radically change the situation. Services that use plain text password transfer are used throughout  . Therefore sniffat for a long time will be
. Therefore sniffat for a long time will be  .
.
Windows implementation of sniffers
CommView - www.tamos.com
A fairly advanced sniffer produced by TamoSoft. You can set your own rules for sniffing (for example, ignore ICMP, and TCP sniff, and besides Internet protocols there is support for Ethernet protocols such as ARP, SNMP, NOVELL, etc.). You can, for example, sniff only incoming packets, and ignore the rest. You can specify a log file for all packages with size limits in the frames. Has two tools - Packet Generator and NIC Vendor Indentifier. You can see all the details of the sent / received packets (for example, in the TCP packet, you can see Source Port, Destination Port, Data length, Checksum, Sequence, Window, Ack, Flags, Urgent). Another good thing is that it automatically installs the CAPTURE driver. In general, the tool is very useful for the sniff, I recommend it to everyone.
SpyNet - packetstorm.securify.com
A fairly well-known sniffer produced by Laurentiu Nicula 2000  . Common functions are intercepting / decoding packets. Although decoding is developed prikolno (it is possible for example on packets to recreate pages on which the user has visited!). In general, for an amateur
. Common functions are intercepting / decoding packets. Although decoding is developed prikolno (it is possible for example on packets to recreate pages on which the user has visited!). In general, for an amateur  .
.
Analyzer - neworder.box.sk
Analyzer requires the installation of a special driver, nested in the package (packet.inf, packet.sys). You can see all the information about your network card. Analyzer also supports the command line. It works fine with a local network. Has several utilities: ConvDump, GnuPlot, FlowsDet, Analisys Engine. Nothing outstanding.
IRIS - www.eeye.com
IRIS is a product of the well-known firm eEye. Represents extensive filtering capabilities. I was very pleased with him in three chips:
1.Protocol Distribution
2.Top hosts
3.Size Distribution
There is also a Packet Decoder. It supports a well-developed system of logs. And the available filtering capabilities are superior to all sniffer browsers. This is a Hardware Filter that can catch either all packages (Promiscious), or with various restrictions (for example, capture only multicast packets or broadcast packets, or only Mac frames). You can filter by specific MAC / IP addresses, by ports, by packets containing certain characters. In general, a good sniffak. Requires 50comupd.dll.
WinDUMP Analog TCPdump for Unix. This sniffak acts through the command line and represents minimal configuration capabilities and still requires the WinPcap library. I'm not very ...
SniffitNT
Also requires WinPcap. Work only as a command line, and in an interactive mode. With complex options. I do not really.
ButtSniff
The usual packet sniffer created by the famous group CDC (Cult of the Dead Cow). The chip of it is that it can be used as a plug-in to BO  (Very helpful
(Very helpful  ). Work from the command line.
). Work from the command line.
There are many more sniffers, such as NatasX, NetXRay, CooperSniffer, LanExplorer, Net Analyzer, etc. Let's go further ...
Unix sniffers
All sniffers of this review can be found on packetstorm.securify.com .
Linsniffer
This is a simple sniffer for capturing logins / passwords. Standard compilation (gcc -o linsniffer linsniffer.c).
The log writes to tcp.log.
Linux_sniffer
Linux_sniffer is required when you want to explore the network in detail. Standard compilation. Gives any shnyagu additionally, such as isn, ack, syn, echo_request (ping), etc.
Sniffit
Sniffit is an advanced sniffer model written by Brecht Claerhout. Install (libcap is needed): #. / Configure
#make
Now run the sniffer:
#. / Sniffit
Usage: ./sniffit [-xdabvnN] [-P proto] [-A char] [-p port] [(-r | -R) recordfile]
[-l sniflen] [-L logparam] [-F snifdevice] [-M plugin]
[-D tty] (-t <Target IP> | -s <Source IP>) | (-i | -I) | -c <config file>]
Plugins Available:
0 - Dummy Plugin
1 - DNS Plugin
As you can see, the sniffet supports many options. You can use sniffak interactively. Sniff though a fairly useful program, but I do not use it. Why? Because Sniffit has big problems with protection. For Sniffit'a there have already been a release root and dos for Linux and debian! Not every sniffer allows himself this allows  .
.
HUNT
This is my favorite sniffak. It is very easy to use, it supports a lot of cool chips and at the moment has no security problems. Plus, it's not particularly demanding on libraries (like linsniffer and Linux_sniffer). It can in real time intercept current connections and under a clean dump from a remote terminal. In general, Hijack rulezzz  . I recommend everyone for enhanced use
. I recommend everyone for enhanced use  . Install:
. Install:
#make
Run:
#hunt -i [interface]
READSMB
Sniffer READSMB is cut from LophtCrack and ported to Unix (oddly enough  ). Readsmb intercepts SMB packets.
). Readsmb intercepts SMB packets.
TCPDUMP
Tcpdump is a fairly well-known packet analyzer. Written by an even more famous brow - Van Jacobson, who came up with VJ-compression for PPP and wrote a prog traceroute (and who knows what else?). Requires the Libpcap library.
Install:
#. / Configure
#make
Now run it:
#tcpdump
Tcpdump: listening on ppp0
All your connections are output to the terminal. Here is an example of ping output
ftp.technotronic.com:
02:03:08.918959 195.170.212.151.1039 > 195.170.212.77.domain: 60946+ A?
ftp.technotronic.com. (38)
02:03:09.456780 195.170.212.77.domain > 195.170.212.151.1039: 60946* 1/3/3 (165)
02:03:09.459421 195.170.212.151 > 209.100.46.7: icmp: echo request
02:03:09.996780 209.100.46.7 > 195.170.212.151: icmp: echo reply
02:03:10.456864 195.170.212.151 > 209.100.46.7: icmp: echo request
02:03:10.906779 209.100.46.7 > 195.170.212.151: icmp: echo reply
02:03:11.456846 195.170.212.151 > 209.100.46.7: icmp: echo request
02:03:11.966786 209.100.46.7 > 195.170.212.151: icmp: echo reply In general, Sniff is useful for debugging networks, troubleshooting, etc.
Dsniff
Dsniff requires libpcap, ibnet, libnids and OpenSSH. Writes only the entered commands, which is very convenient. Here is an example of a connectivity log on unix-shells.com:
02/18/01 3:58:04 tcp my.ip.1501 -> handi4-145-253-158-170.arcor-ip.net.23
(Telnet)
Stalsen
Asdqwe123
Ls
Pwd
Who
Last
Exit
Here dsniff intercepted the login with the password (stalsen / asdqwe123). Install:
#. / Configure
#make
#make install
Protection against sniffers
The surest way to protect against sniffers is to use ENCRYPTION (SSH, Kerberous, VPN, S / Key, S / MIME, SHTTP, SSL, etc.). Well, if you do not want to refuse plain text services and install additional packages  ? Then it's time to use antisnifferskie pekety ...
? Then it's time to use antisnifferskie pekety ...
AntiSniff for Windows
This product was released by the famous Lopht group. It was the first product of its kind. AntiSniff, as stated in the description:
"AntiSniff is a Graphical User Interface (GUI) -based tool for detecting promiscuous Network Interface Cards (NICs) on your local network segment." In general, it catches cards in promisc mode, supports a huge number of tests (DNS test, ARP test, Ping Test , ICMP Time Delta Test, Echo Test, PingDrop test.) It is possible to scan both a single machine and a grid, where there is logging support.) AntiSniff works on win95 / 98 / NT / 2000, although the recommended NT platform. Already in a short time there was a sniffer called AntiAntiSniffer  , Written by Mike Perry (found at www.void.ru/news/9908/snoof.txt ). It is based on LinSniffer (discussed below).
, Written by Mike Perry (found at www.void.ru/news/9908/snoof.txt ). It is based on LinSniffer (discussed below).
Unix sniffer detect:
Sniffer can be detected by the command:
#ifconfig -a
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
UP LOOPBACK RUNNING MTU:3924 Metric:1
RX packets:2373 errors:0 dropped:0 overruns:0 frame:0
TX packets:2373 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
ppp0 Link encap:Point-to-Point Protocol
inet addr:195.170.yx PtP:195.170.yx Mask:255.255.255.255
UP POINTOPOINT PROMISC RUNNING NOARP MULTICAST MTU:1500 Metric:1
RX packets:3281 errors:74 dropped:0 overruns:0 frame:74
TX packets:3398 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:10 As you can see, the ppp0 interface is in PROMISC mode. Either the operator uploaded the sniff to check the network, or you already have ... But remember that ifconfig can be easily changed, so use tripwire to detect changes and all the bugs to check for sniffs.
AntiSniff for Unix.
Works on BSD, Solaris and Linux. It supports ping / icmp time test, arp test, echo test, dns test, ethering test, in general, AntiSniff for Win, only for Unix  . Install:
. Install:
#make linux-all
Sentinel
Also a useful program for catching sniffers. Supports many tests. Easy to use. Install: #make
#. / Sentinel
./sentinel [method] [-t <target ip>] [options]
Methods:
[-a ARP test]
[-d DNS test]
[-i ICMP Ping Latency test]
[-e ICMP Etherping test]
Options:
[-f <non-existant host>]
[-v Show version and exit]
[-n <number of packets / seconds>]
[-I <device>]
The options are so simple that no comments.
MORE
Here are a few more utilities to test your network (for Unix):
Packetstorm.securify.com/UNIX/IDS/scanpromisc.c - PROMISC mode for ethernet cards (for red hat 5.x).
Http://packetstorm.securify.com/UNIX/IDS/neped.c - Network Promiscuous Ethernet Detector (libcap & Glibc needed).
Http://packetstorm.securify.com/Exploit_Code_Archive/promisc.c -Contains the system's devices to detect sniffs.
Http://packetstorm.securify.com/UNIX/IDS/ifstatus2.2.tar.gz - ifstatus tests network interfaces in PROMISC mode.
Via xakep.ru


Comments
Commenting on, remember that the content and tone of your message can hurt the feelings of real people, show respect and tolerance to your interlocutors even if you do not share their opinion, your behavior in the conditions of freedom of expression and anonymity provided by the Internet, changes Not only virtual, but also the real world. All comments are hidden from the index, spam is controlled.